- HSM
- Shredding
- Other
- Information about data protection
- Legal
- Destroying data legal basis
Destroying data securely - Legal basis
The General Data Protection Regulation (GDPR) has been in force in Europe since May 2018. It standardizes the handling of personal data by companies. This handling includes, on the one hand, the storage and, on the other hand, the compliant deletion of this data. Secure and data protection-compliant data destruction plays an important role, especially in the commercial environment, since the collection of personal data has increased enormously in recent years. Thus, on the one hand, legal data retention periods apply and, on the other hand, there is the right to the deletion of personal data.

Destroying data securely - main points
The General Data Protection Regulation stipulates that personal data may only be stored for as long as necessary for the purpose for which they were collected. This means that the data must be deleted after the purpose has been fulfilled, unless legal or contractual retention periods apply (Art. 5 para. 1 e) GDPR).
The right of deletion
Pursuant to Article 17 paragraph 1 GDPR, data subjects have the right to have their personal data deleted / the data subject has the right to have their personal data deleted. This means that the person concerned can demand that the person responsible immediately deletes his/her personal data.
When personal data are deleted, it is generally sufficient if the data carriers containing the data to be deleted are physically destroyed. This is because the destruction of data carriers is also a form of deletion.
However, it is NOT sufficient if the data carriers are simply disposed of, i.e. thrown into the rubbish bin.
Destroying data securely - Types of data carriers
Different types of data carriers may be used for the storage of personal or other sensitive data:
- P: data carriers in paper form such as files or entire folders
- O: optical data carriers such as CDs, DVDs
- T: magnetic data carriers such as magnetic cards or floppy disks
- E: electronic data carriers such as USB sticks or chip cards
- F: information in reduced form for instance film rolls or foil
- H: hard drives with magnetic media
Daten sicher vernichten - Vernichtung von Datenträgern
Irrespective of the choice of the data carrier used, its deletion or destruction in accordance with data protection laws applies.
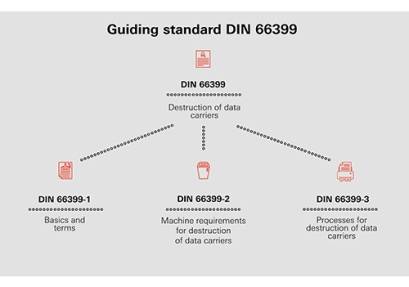
The destruction of these data carriers is subject to the guiding standard DIN 66399, which is divided into three parts:
DIN 66399-1:
Here, basics such as protection requirements, protection classes and security levels are explained. The appropriate security level depends on the level of protection required for the data to be destroyed. HSM recommends a shredder in security level P-4 or higher for data carriers with particularly sensitive and confidential data as well as personal data that is subject to an increased need for protection, e.g. balance sheets, pay slips, personnel files, employment contracts and tax documents, for data in paper form.
Read more about this on our page Protection Classes and Security Levels.
DIN 66399-2:
The second part of the leading standard DIN 66399 regulates the classification of data carriers and the applicable machine requirements.
DIN 66399-3:
The third part of the standard describes three different processes for the destruction of data media:
- the data carriers are destroyed by the responsible body itself
- the data media are destroyed by a service provider at the facilities of the responsible body
- the data carriers are destroyed by a service provider at an external location
You can read about the advantages of in-house data destruction on our page Internal vs. External Data Destruction.
Destroying data securely - Expert recommendation
In order to correctly implement the DIN 66399 standard, HSM recommends an in-house data destruction, i.e. the destruction of personal data directly at the point of origin.
Depending on the type of data carrier to be destroyed and the need for protection of the data on it, the purchase of a document / media shredder with a minimum security level of P-4/H-4 is recommended. However, the purchase of a separate media shredder is often not necessary, as modern document shredders, depending on their features, destroy almost everything - paper, CDs, ID cards, USB sticks, chip cards, flash memory, films and foils.
Here, too, different protection classes and security levels with different particle sizes apply to the destruction, depending on the security requirements.
